2021寒假MISC打卡DAY12
作者:互联网
- [INSHack2017]sanity
签到题
# Challenge description:
I really hope you are INSAne, but if that's not the case and that you don't want to validate the "INSAnity" challenge then maybe you would like to validate this one? Here is your flag, you disapointing and boring fellow: INSA{Youre_sane_Good_for_you}
得到的 flag 请包上 flag{} 提交
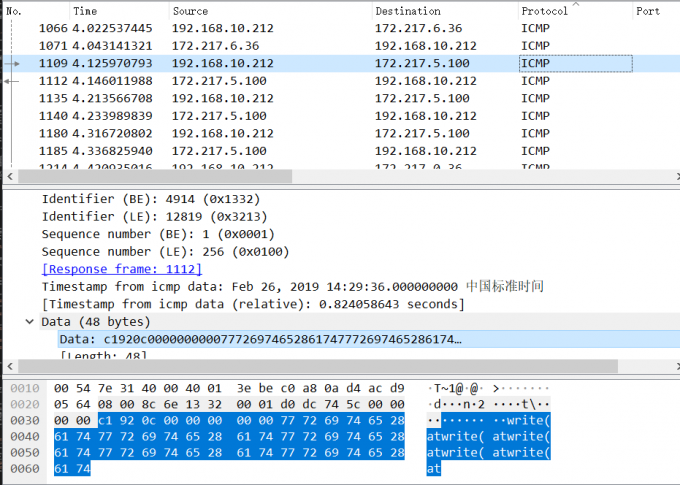
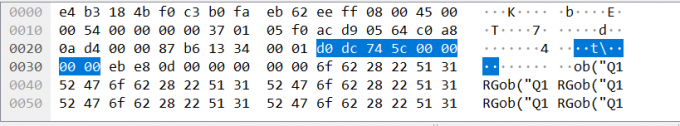
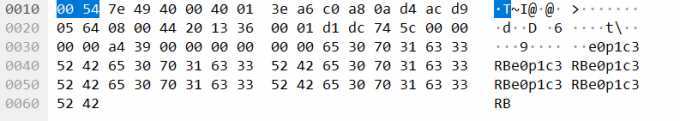
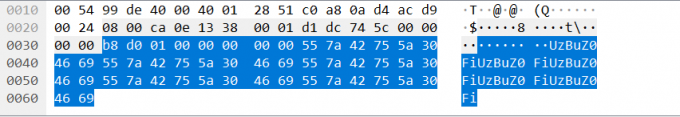
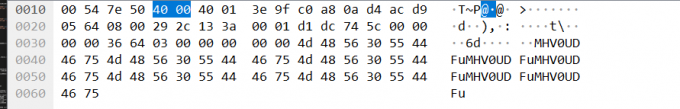
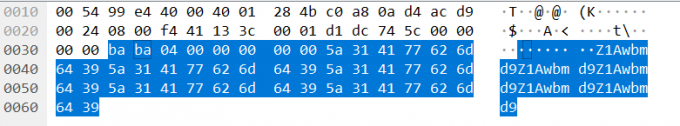
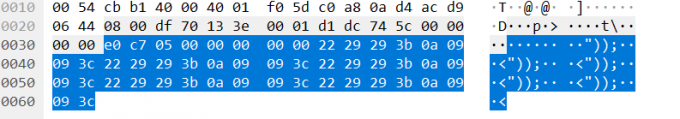
注意到ICMP流中出现了
writeat(ob("Q1RGe0p1c3RBUzBuZ0FiMHV0UDFuZ1Awbmd9"));
base64解码
CTF{JustAS0ngAb0utP1ngP0ng}
- [MRCTF2020]小O的考研复试
一道数学题
22…2(19260817个2对(1e9+7)取模
分成两步,求整数和取余
a=2
for i in range(19260816):
a = a * 10 + 2
a%=(1e9+7)
计算得
flag{577302567}
4. [INSHack2019]INSAnity
签到题
INSA{YouRe_Crazy_and_I_Love_it}
5. [INSHack2017]insanity
We dare you to validate this challenge that will REALLY remove 2pts from your score! If you really are crazy, then here is your flag: INSA{Youre_crazy_I_like_it}
- [INSHack2019]Sanity
INSA{Welcome} - [CFI-CTF 2018]webLogon capture
啊这,今天做的几题这么无脑的吗
{"email":"test@example","password":"%20%43%46%49%7b%31%6e%73%33%63%75%72%33%5f%6c%30%67%30%6e%7d%20"}
urldecode
CFI{1ns3cur3_l0g0n}
8. >key不在这里(https://buuoj.cn/challenges#key%E4%B8%8D%E5%9C%A8%E8%BF%99%E9%87%8C)
注意:得到的 flag 请包上 flag{} 提交
一张二维码,扫码得
https://cn.bing.com/search?q=key%E4%B8%8D%E5%9C%A8%E8%BF%99%E9%87%8C&m=10210897103375566531005253102975053545155505050521025256555254995410298561015151985150375568&qs=n&form=QBRE&sp=-1&sc=0-38&sk=&cvid=2CE15329C18147CBA4C1CA97C8E1BB8C
直接搜索无所得
观察得,102,108,97,103等老朋友
十进制转ascii
urldecode
flag{5d45fa256372224f48746c6fb8e33b32}
-
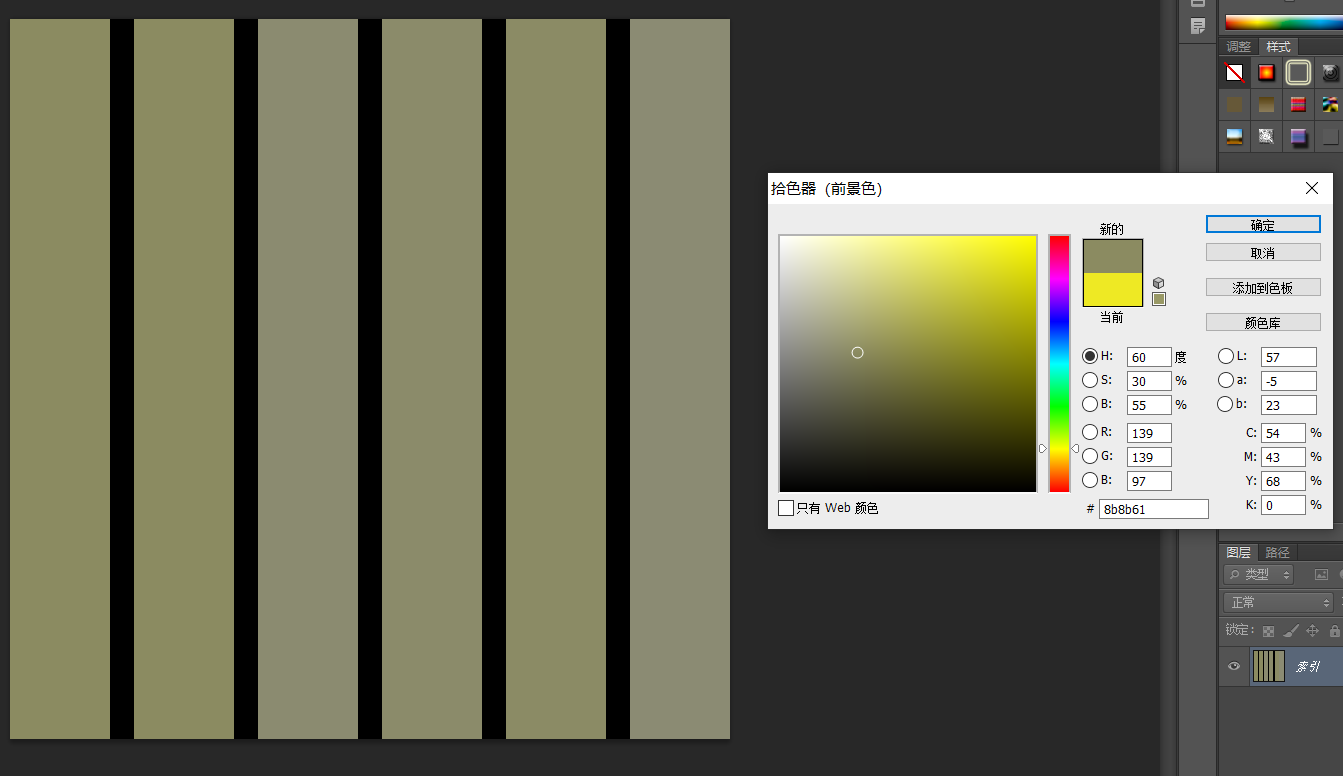
很好的色彩呃?
注意:得到的 flag 请包上 flag{} 提交
根据题目提示:颜色
打开PS,取色器提取颜色的十六进制
分别为
8b8b61
8b8b61
8b8b70
8b8b6a
8b8b65
8b8b73
>>6161706A6573
HEX>>
aapjes
flag{aapjes}
-
[GUET-CTF2019]520的暗示(https://buuoj.cn/challenges#[GUET-CTF2019]520%E7%9A%84%E6%9A%97%E7%A4%BA)
注意:得到的 flag 请包上 flag{} 提交
得到photo.dat,与0x33异或
data = open("photo.dat",'rb')
strs = data.read()
flag = open("1.jpg",'ab+')
for i in strs:
flag.write(bytes([i ^ 0x33]))
得到一张运营商的定位
根据LTE可以定位基站地址http://www.gpsspg.com/bs.htm
flag{桂林电子科技大学花江校区}
妙啊
标签:INSA,cn,包上,MISC,flag,2021,https,打卡,your 来源: https://blog.csdn.net/LLKJSAF/article/details/114163407