使用 DEVOPS CLI 创建服务连接
作者:互联网
向我的技术倡导者和专家同事致以问候。
在此会话中,我将演示如何使用 DevOps CLI 创建服务连接。
| 使用案例:- |
|---|
| 创建DevOps服务连接,提示PAT(个人访问令牌) |
| 创建DevOps服务连接,无需提示PAT(个人访问令牌) |
| 自动化目标:- |
|---|
| 创建服务主体。 |
| 查询服务主体的应用程序 ID。 |
| 将服务主体应用程序 ID 和机密存储在密钥保管库中。 |
| 在订阅级别分配服务主体“参与者”RBAC(基于角色的访问控制)。 |
| 将服务主体机密设置为用于创建 Azure DevOps 服务连接的环境变量。 |
| 将PAT(个人访问令牌)设置为DevOps 登录的环境变量。 |
| 创建Azure DevOps Service Connection。 |
| 向新创建的 Azure DevOps 服务连接授予对所有管道的访问权限。 |
| 验证服务连接。 |
| 要求:- |
|---|
- Azure 订阅。
- Azure DevOps 组织和项目。
- 完全访问 PAT(个人访问令牌)。
- 执行脚本的标识具有以下权限:a) 在 Azure Active Directory 中创建服务主体、b) 分配 RBAC 和 c) 在密钥保管库中创建机密。
使用 DEVOPS CLI 创建服务连接使用 DEVOPS CLI 创建服务连接向我的技术倡导者和专家同事致以问候。 在此会话中,我将演示如何使用 DevOps CLI 创建服务连接。
|
| 以下是代码片段:- |
|---|
| 用例 #1:- |
|---|
| 使用 PAT 作为用户输入创建 AZURE DEVOPS SERVICE CONNECTION (CREATE-DevOps-service-connection-prompt-pat.ps1):- |
|---|
##############
# VARIABLES:-
##############
$spiname = "AM-Test-SPI-100"
$rbac = "Contributor"
$devopsOrg = "https://dev.azure.com/arindammitra0251/"
$devopsPrj = "AMCLOUD"
$subsID = "210e66cb-55cf-424e-8daa-6cad804ab604"
$subsName = "AM-PROD-VS"
$tenantID = "20516b3d-42af-4bd4-b2e6-e6b4051af72a"
$kv = "ampockv"
##############
# CORE SCRIPT:-
##############
# Create Service Principal and Store Secret in a variable:-
$spipasswd = az ad sp create-for-rbac -n $spiname --query "password" -o tsv
# Query the Application ID of the Service Principal and Store it in a variable:-
$spiID = az ad sp list --display-name $spiname --query [].appId -o tsv
# Store the Service Principal Application ID and Secret in Key Vault:-
az keyvault secret set --name $spiname-id --vault-name $kv --value $spiID
az keyvault secret set --name $spiname-passwd --vault-name $kv --value $spipasswd
# Assign the Service Principal, "Contributor" RBAC on Subscription Level:-
az role assignment create --assignee "$spiID" --role "$rbac" --scope "/subscriptions/$subsID"
#Set Service Principal Secret as an Environment Variable for creating Azure DevOps Service Connection:-
$env:AZURE_DEVOPS_EXT_AZURE_RM_SERVICE_PRINCIPAL_KEY=$spipasswd
# Perform DevOps Login. It will Prompt for PAT:-
az devops login
# Set Default DevOps Organisation and Project:-
az devops configure --defaults organization=$devopsOrg project=$devopsPrj
# Create DevOps Service Connection:-
az devops service-endpoint azurerm create --azure-rm-service-principal-id $spiID --azure-rm-subscription-id $subsID --azure-rm-subscription-name $subsName --azure-rm-tenant-id $tenantID --name $spiname --org $devopsOrg --project $devopsPrj
# Grant Access to all Pipelines to the Newly Created DevOps Service Connection:-
$srvEndpointID = az devops service-endpoint list --query "[?name=='$spiname'].id" -o tsv
az devops service-endpoint update --id $srvEndpointID --enable-for-all
| 用例 #2:- |
|---|
| 使用 PAT 作为环境变量创建 AZURE DEVOPS SERVICE CONNECTION (CREATE-DevOps-service-connection-without-prompting-pat.ps1):- |
|---|
##############
# VARIABLES:-
##############
$spiname = "AM-Test-SPI-200"
$rbac = "Contributor"
$pat = "<Provide your own PAT>"
$devopsOrg = "https://dev.azure.com/arindammitra0251/"
$devopsPrj = "AMCLOUD"
$subsID = "210e66cb-55cf-424e-8daa-6cad804ab604"
$subsName = "AM-PROD-VS"
$tenantID = "20516b3d-42af-4bd4-b2e6-e6b4051af72a"
$kv = "ampockv"
##############
# CORE SCRIPT:-
##############
# Create Service Principal and Store Secret in a variable:-
$spipasswd = az ad sp create-for-rbac -n $spiname --query "password" -o tsv
# Query the Application ID of the Service Principal and Store it in a variable:-
$spiID = az ad sp list --display-name $spiname --query [].appId -o tsv
# Store the Service Principal Application ID and Secret in Key Vault:-
az keyvault secret set --name $spiname-id --vault-name $kv --value $spiID
az keyvault secret set --name $spiname-passwd --vault-name $kv --value $spipasswd
# Assign the Service Principal, "Contributor" RBAC on Subscription Level:-
az role assignment create --assignee "$spiID" --role "$rbac" --scope "/subscriptions/$subsID"
#Set Service Principal Secret as an Environment Variable for creating Azure DevOps Service Connection:-
$env:AZURE_DEVOPS_EXT_AZURE_RM_SERVICE_PRINCIPAL_KEY=$spipasswd
# Set PAT as an environment variable for DevOps Login:-
$env:AZURE_DEVOPS_EXT_PAT = $pat
# Set Default DevOps Organisation and Project:-
az devops configure --defaults organization=$devopsOrg project=$devopsPrj
# Create DevOps Service Connection:-
az devops service-endpoint azurerm create --azure-rm-service-principal-id $spiID --azure-rm-subscription-id $subsID --azure-rm-subscription-name $subsName --azure-rm-tenant-id $tenantID --name $spiname --org $devopsOrg --project $devopsPrj
# Grant Access to all Pipelines to the Newly Created DevOps Service Connection:-
$srvEndpointID = az devops service-endpoint list --query "[?name=='$spiname'].id" -o tsv
az devops service-endpoint update --id $srvEndpointID --enable-for-all
| DIFFERENCE BETWEEN BOTH USE CASES:- |
|---|
| In Use Case 1, PAT is prompted as User Input during script execution. |
| In Use Case 2, PAT is set as Environment variable so that it is not prompted as User Input during script execution. |
Now, let me explain the script, part by part for better understanding.
| VARIABLES:- |
|---|
USE CASE 1:-
##############
# VARIABLES:-
##############
$spiname = "AM-Test-SPI-100"
$rbac = "Contributor"
$devopsOrg = "https://dev.azure.com/arindammitra0251/"
$devopsPrj = "AMCLOUD"
$subsID = "210e66cb-55cf-424e-8daa-6cad804ab604"
$subsName = "AM-PROD-VS"
$tenantID = "20516b3d-42af-4bd4-b2e6-e6b4051af72a"
$kv = "ampockv"
USE CASE 2:-
##############
# VARIABLES:-
##############
$spiname = "AM-Test-SPI-200"
$rbac = "Contributor"
$pat = "<Provide your own PAT>"
$devopsOrg = "https://dev.azure.com/arindammitra0251/"
$devopsPrj = "AMCLOUD"
$subsID = "210e66cb-55cf-424e-8daa-6cad804ab604"
$subsName = "AM-PROD-VS"
$tenantID = "20516b3d-42af-4bd4-b2e6-e6b4051af72a"
$kv = "ampockv"
| NOTE:- |
|---|
| Please change the values of the variables accordingly. |
| The entire script is build using Variables. No Values are Hardcoded. Changing the values of the variables should help you execute the script seamlessly. |
| CORE SCRIPT:- |
|---|
Create Service Principal and Store Secret in a variable:-
$spipasswd = az ad sp create-for-rbac -n $spiname --query "password" -o tsv
Query the Application ID of the Service Principal and Store it in a variable:-
$spiID = az ad sp list --display-name $spiname --query [].appId -o tsv
Store the Service Principal Application ID and Secret in Key Vault:-
az keyvault secret set --name $spiname-id --vault-name $kv --value $spiID
az keyvault secret set --name $spiname-passwd --vault-name $kv --value $spipasswd
Assign the Service Principal, "Contributor" RBAC on Subscription Level:-
az role assignment create --assignee "$spiID" --role "$rbac" --scope "/subscriptions/$subsID"
Set Service Principal Secret as an Environment Variable for creating Azure DevOps Service Connection:-
$env:AZURE_DEVOPS_EXT_AZURE_RM_SERVICE_PRINCIPAL_KEY=$spipasswd
Perform DevOps Login. It will Prompt for PAT Token:-
az devops login
OR
Set PAT as an environment variable for DevOps Login:-
$env:AZURE_DEVOPS_EXT_PAT = $pat
Set Default DevOps Organisation and Project:-
az devops configure --defaults organization=$devopsOrg project=$devopsPrj
Create DevOps Service Connection:-
az devops service-endpoint azurerm create --azure-rm-service-principal-id $spiID --azure-rm-subscription-id $subsID --azure-rm-subscription-name $subsName --azure-rm-tenant-id $tenantID --name $spiname --org $devopsOrg --project $devopsPrj
Grant Access to all Pipelines to the Newly Created DevOps Service Connection:-
$srvEndpointID = az devops service-endpoint list --query "[?name=='$spiname'].id" -o tsv
az devops service-endpoint update --id $srvEndpointID --enable-for-all
NOW ITS TIME TO TEST
| TEST CASES:- |
|---|
| TEST CASE FOR USE CASE #1: PAT AS USER INPUT:- |
|---|
| Service Principal has been created. Application ID and Secret has been Stored in Key Vault. "Contributor" RBAC has been assigned to the newly created Service Principal on Subscription Level. |
| As Observed, the script is now waiting for User Input PAT. |
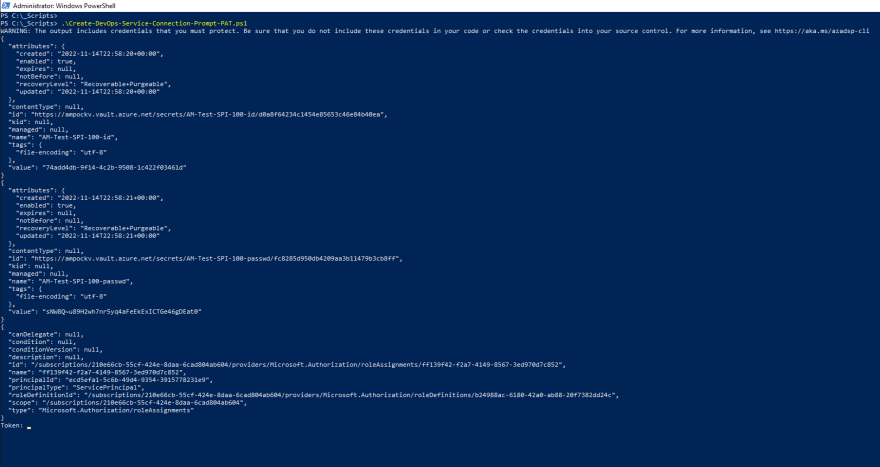 |
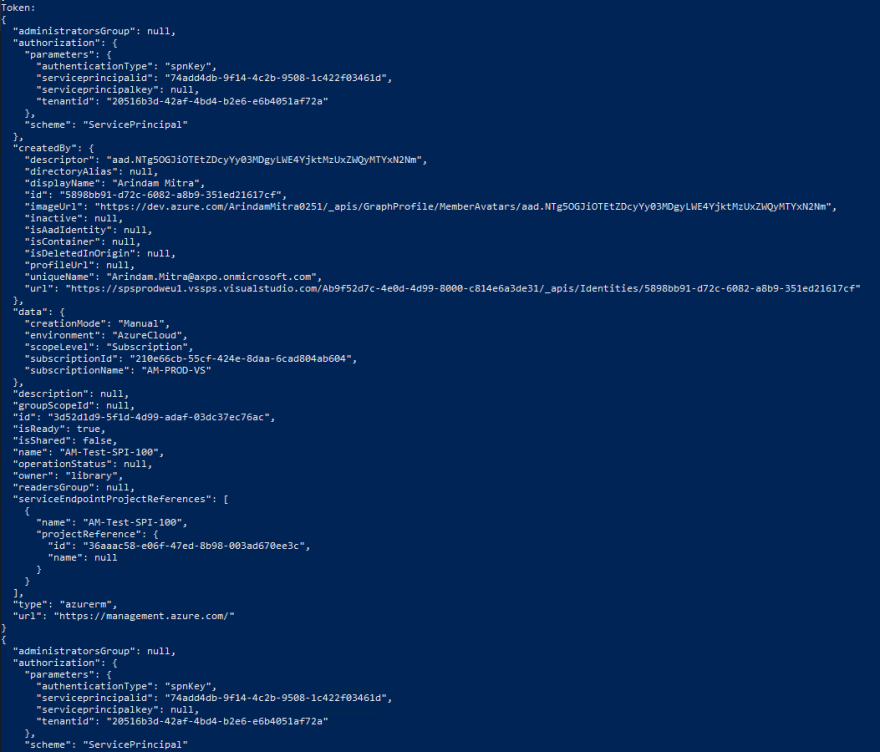
| After providing the correct PAT, script executed successfully. |
 |
 |
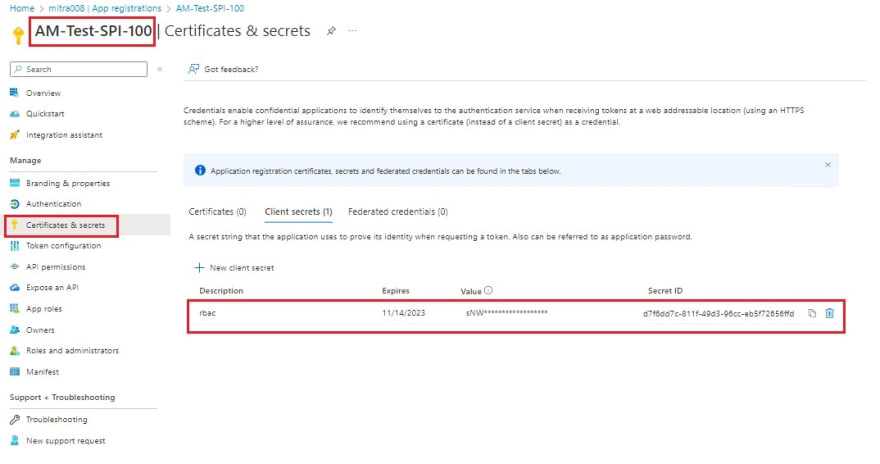
| Service Principal (with secret) created successfully. |
 |
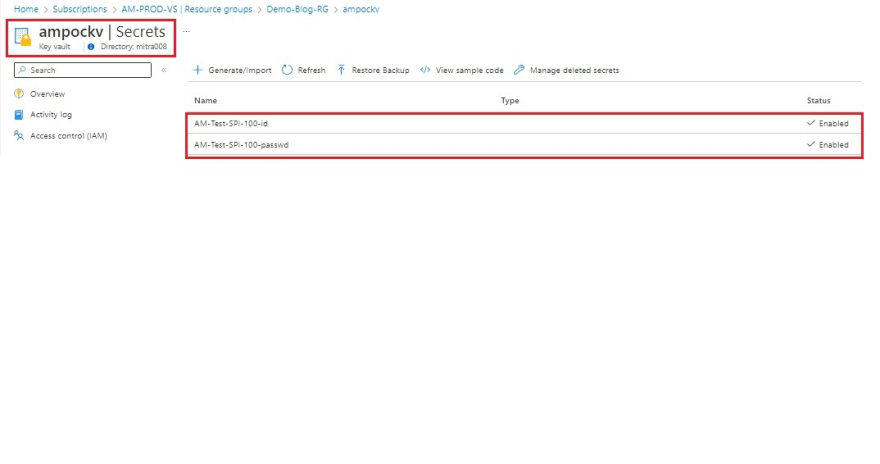
| Application ID and Secret of Service Principal has been stored in Key Vault. |
 |
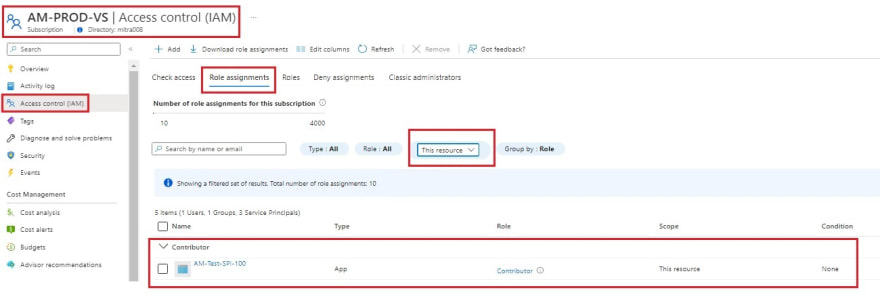
| "Contributor" RBAC has been assigned to the newly created Service Principal on Subscription Level. |
 |
| Azure DevOps Service Connection has been created successfully with the newly created Service Principal. |
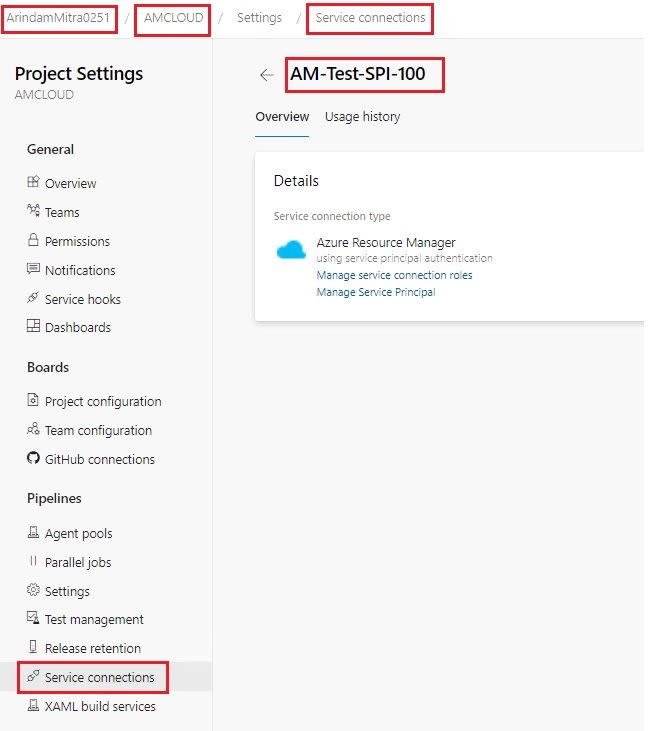 |
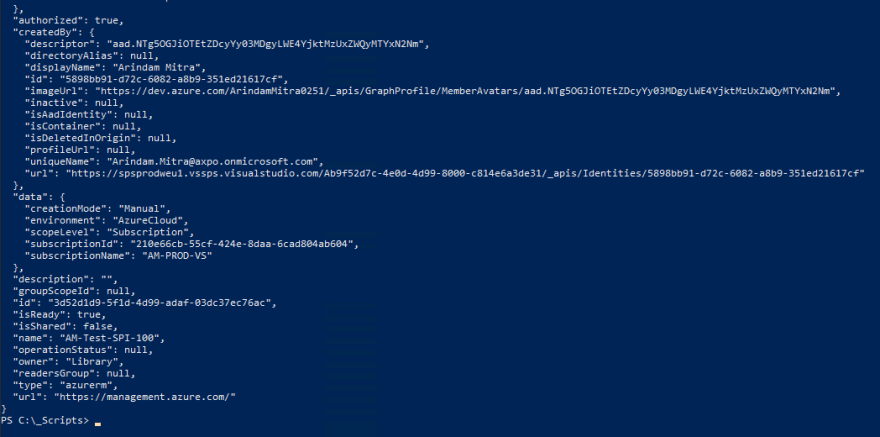
| Azure DevOps Service Connection Verification is successful. |
 |
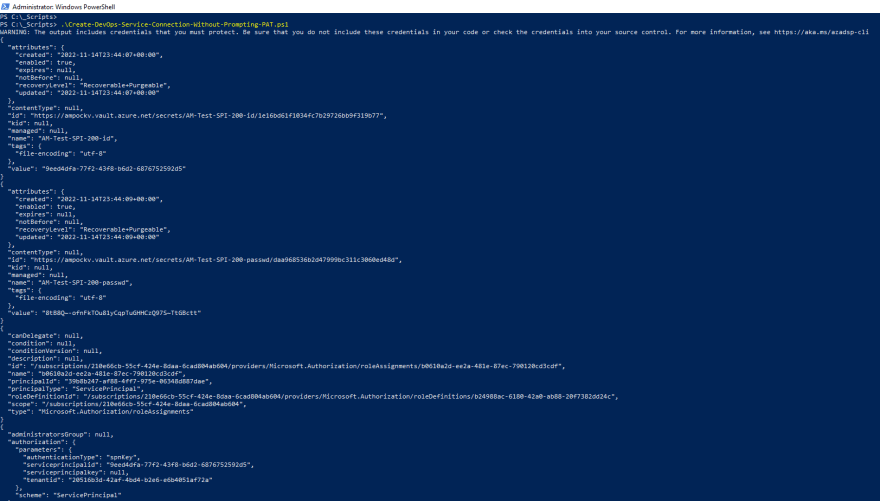
| TEST CASE FOR USE CASE #2: PAT AS ENVIRONMENT VARIABLE:- |
|---|
| Service Principal has been created. Application ID and Secret has been Stored in Key Vault. "Contributor" RBAC has been assigned to the newly created Service Principal on Subscription Level. |
| As Observed, No PAT is prompted during script execution. |
 |
 |
 |
| Service Principal (with secret) created successfully. |
 |
| Application ID and Secret of Service Principal has been stored in Key Vault. |
 |
| “贡献者”RBAC 已分配给订阅级别新创建的服务主体。 |
 |
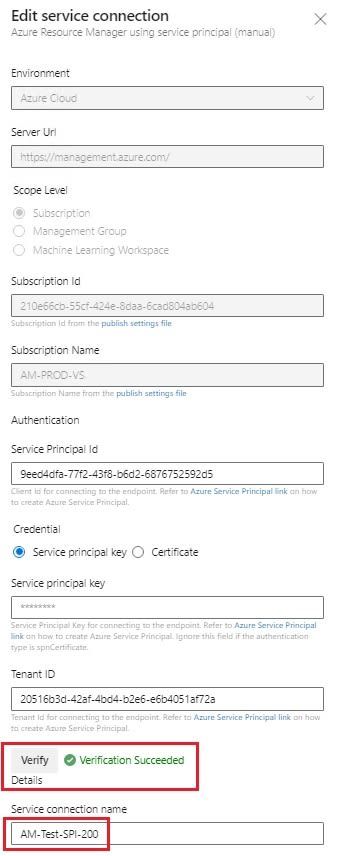
| Azure DevOps 服务连接已成功创建,使用新创建的服务主体。 |
 |
| Azure DevOps 服务连接验证成功。 |
 |
希望您喜欢这次会议!!!
|保持安全继续学习|传播知
更新您的开发经验级别:
转到自定义设置,轻推首页 Feed,以显示与您的开发者体验水平更相关的内容。